Tactical Management
Solutions for secure, easy, and effective network and device management
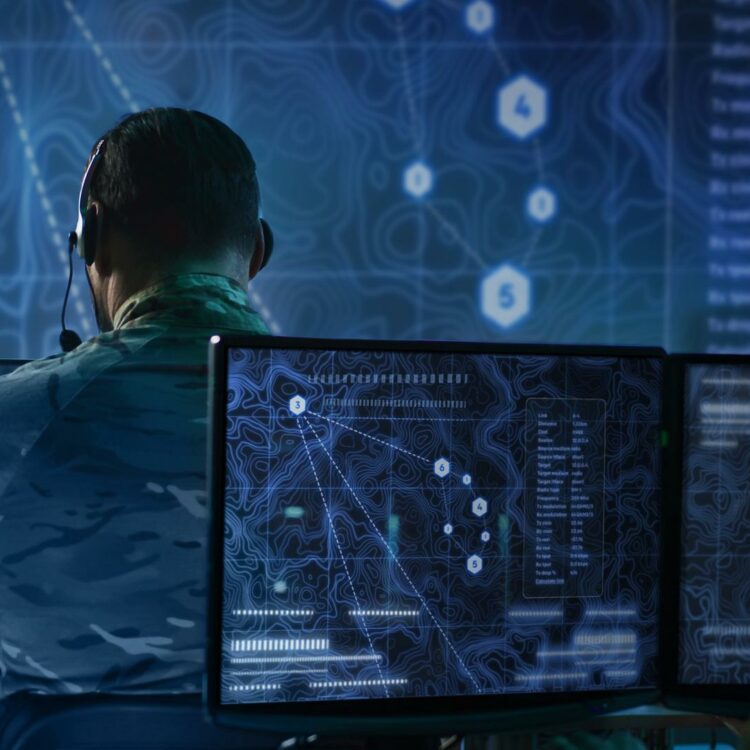
Manage Tactical Devices & Networks from Depot to Deployment
With Bittium’s advanced tactical communication devices and systems it is possible to form tactical networks that provide resilient connectivity and best performance across the battlefield.
For taking the devices and networks from depot to deployment and beyond, take advantage of Bittium Tactical Management Suite™, including Bittium Tactical Device Management™ and Bittium Tactical Network Management™ systems. The systems provide advanced tools for secure and effective device and network management.
Secure Management of Tactical Devices Prior, During, and After Deployment
Bittium Tactical Device Management™ (TDM) is an advanced and easy-to-use management system for Bittium’s tactical communication devices, including at the first stage Bittium Tough SDR™ radios.
With TDM, it is easy to initialize and prepare the radios for missions, as well as manage the radios effectively during operations.


Effective Planning, Management & Analysis of Tactical Networks
Bittium Tactical Network Management™ toolset is used with Bittium’s tactical networks and nodes to enable intuitive and visual network planning, real-time management of the networks, and performance analysis based on big data collected from the network. This enables quick and effective deployment of the networks and successful operations.