Current and Future Security Threats to Medical Devices and Systems

Current and Future Security Threats to Medical Devices and Systems
Author: Hannu Juopperi, Security Architect, Bittium
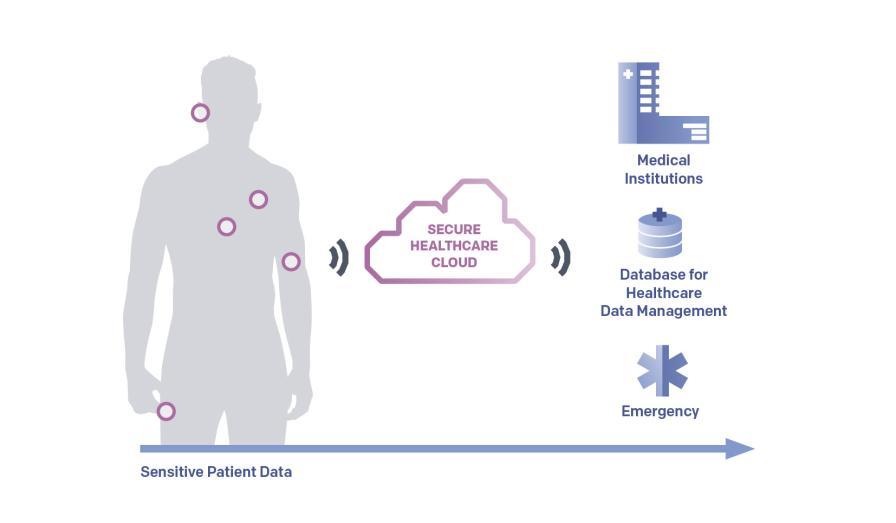
The Internet of Things (IoT) has already penetrated numerous industries, and the healthcare industry is no exception. Connected medical devices and systems, which can collect, transmit and store important health data, open up new possibilities for patient monitoring and remote medical treatment options. These solutions help to tackle challenges such as medical staff shortages and rising healthcare costs with quicker diagnosis and treatment while offering also more comfort for the patient.
Given these future prospects, the global medical devices market is expected to grow from USD 455.34 billion in 2021 to USD 657.98 billion in 2028 [1]. The enormous potential for developers and manufacturers however comes with some severe challenges. The most obvious and most broadly discussed one is security – especially since security flaws in a connected device can open a gateway for cyber criminals into a much broader network. Our R&D team specializes on tackling such challenges together with our clients and partners, and we have summarized some key threats that medical device and system designers should take into account.
The German Federal Office for Information Security (BSI) recently investigated the extent to which medical devices are at risk [2]. The experts checked various medical products for the treatment and care of patients – including randomly selected pacemakers, defibrillators, insulin pumps, ventilators, infusion pumps, patient monitors and home emergency call systems for seniors, which are often used in care and support – with regards to their security. They found ca. 150 vulnerabilities. In a recent research report published by CNN, more than a dozen vulnerabilities in software used in medical devices and machinery by well-known manufacturers were discovered [3]. This increases the risk for hospitals and other facilities: one unpatched security flaw in a single device is enough to compromise the entire network as cyber criminals can work their way into a network step by step.
Even though medical devices already need to comply with at least five to ten evolving security standards, such as several ANSI/AAMI MEE standards, IEC standards or AIM standards, it is possible to see from the examples that there is also a constant need to re-evaluate threats and how to respond to those in product design.
Personally Identifiable Information (PII) at Risk
One of the main security risks is the handling of Personally Identifiable Information. Currently medical devices might not always be considered as devices potentially carrying and collecting PII. Therefore, the data collected and transmitted to the cloud or a network or is not treated under the rules of the EU General Data Protection Regulation (GDPR), California Consumer Privacy Act (CCPA) or Health Insurance Portability and Accountability Act (HIPAA) – which specify how PII data needs to be secured, stored and even professionally destroyed based on specific regulations with regards to the data usage.
Therefore, medical devices collect data that can contain PII and even if this data is deleted from the device itself after usage, the data can often remain on a network or in a cloud environment.
On the one hand this could lead to future compliance issues, if GDPR and/or CCPA regulations will be applied to medical devices with the rapidly evolving Medical Internet of Things (MIoT) market.
On the other hand the unsecured data opens the doors for additional future security threats.
Falsifying and Exploiting Medical Data
As more and more medical data is being collected via IoT devices, we must be absolutely certain that the information is correct and not available for misuse. This means that we need to secure both the data at rest and in transit to be sure that it is not compromised – not just the PII data, but all data collected by medical devices.
If this data is not secured correctly the collected medical data itself could be used for attacks. In a replay attack for example, collected medical data could be replayed to medical authority and thereby falsifying current medical data collection.
The risk is twofold – on the one hand this could be used as a Denial of Service (DoS) attack to incapacitate a medical service provider or a medical authority. On the other hand, this poses a serious risk to a patient´s health as the treating practitioner will not have any knowledge about the patient´s current situation.
Personal Identification Through Biometrics and Biosignals
Today biometrics are known as one of the measures for secure access and often used as a part of even more secure layered authentication. Authentication through fingerprints, facial recognition, or iris scans are used to give access for example to buildings, cars, mobile devices, or data. When it comes to collecting sensitive health information through medical devices and wearables, experts from engineering and technology associations such as IEEE propose to use biometric authentication to secure the access and usage [4]. Additional advantage would be that a smart device recognizes the user and can adapt the service profile – just like the latest generation of cars can identify the driver though biometric recognition and adapt seat and airbag positions for safety, allow access to personal information though the infotainment system, etc.
On the downside, biometrics and also biosignals such as ECG could also be misused. Collecting medical data for longer periods of time can create information profiles that can be used to identify a person. This might sound like science fiction but there are several studies of ECG profiles being used for identification [5]. Taking this a step further: according to a report in the MIT Technology Review, the Pentagon is already testing a laser that can identify people by their heartbeat [6]. Other techniques such as gait analysis, which identifies someone by the way he or she walks, have been used in trying to identify infamous terrorists before a drone strike. But gaits, like faces, are not always distinctive enough for a secure identification. An individual’s cardiac signature however is unique, like an iris or fingerprint. And while there are undoubtedly legitimate scenarios to use a cardiac signature as identifier – there are always options to misuse this information. This brings us back to the reasoning why medical data needs to be treated with the highest security standards.
Highly Individualized Approach Needed to Address the Issues
With the worldwide increase of IoT and MIoT devices – medical wearable and interconnected medical devices which provide remote health monitoring – all experts agree that the security measurements need enhancements. Healthcare data is highly sensitive, and it attracts the attention of attackers [7] and medical devices are a worthwhile target for hackers because they are usually easy to hijack [8]. One of the reasons is the comparatively long lifecycle of the devices. As medical devices have to undergo long certification processes, configuration settings are often frozen at the firmware and operating system version used at the beginning of the certification process. Designers need to find a way to update security measures over the lifetime of the device without compromising the certifications.
An obvious step in the right direction is that healthcare data must be covered under the scope of GDPR, CCPA or HIPAA. Manufacturers and device developers need to understand that the data is PII and needs to be handled as such. Other useful approaches include implementing the “STRIDE” security threat model – Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege. However, due to highly varied designs and use cases of medical devices, there is no single set of means to implement all necessary security measurements. Every device needs to be individually evaluated concerning medical data security. If a medical device manufacturer or engineering team does not have the required R&D expertise and testing facilities in-house, they can always team up with R&D service providers such as Bittium who have the needed know-how.
Find out more about Bittium’s R&D Services for Healthcare and Medical and contact us.
Hannu Juopperi, Security Architect, Bittium
Hannu Juopperi has over 25 years of experience in information technology. He works as a security architect at Bittium and has been with the company since 2017.

References
[1] Fortune Business Insights: Medical Devices Market Size
[2] Cyber-Sicherheitsbetrachtung vernetzter Medizinprodukte BSI-Projekt 392: Manipulation von Medizinprodukten (ManiMed)
[3] CNN Business: Researchers uncover software flaws leaving medical devices vulnerable to hackers
[4] Bio-signals for secure authentification (IEEE)
[5] ECG profiles as identifier
[6] MIT Technology Review: The Pentagon has a laser that can identify people from a distance – by their heartbeat
[7] A Review of Evidence Relating to Harm Resulting from Uses of Health and Biomedical Data https://www.nuffieldbioethics.org/wp-content/uploads/A-Review-of-Evidence-Relating-to-Harms-Resulting-from-Uses-of-Health-and-Biomedical-Data-FINAL.pdf – https://owasp.org/ – IoT-Based Applications in Healthcare Devices
[8] ResearchGate: Broken Heated: How To Attack ECG Biometrics